SSH
The second command in the series is the one I find more useful and versatile so it also will be the longest post.
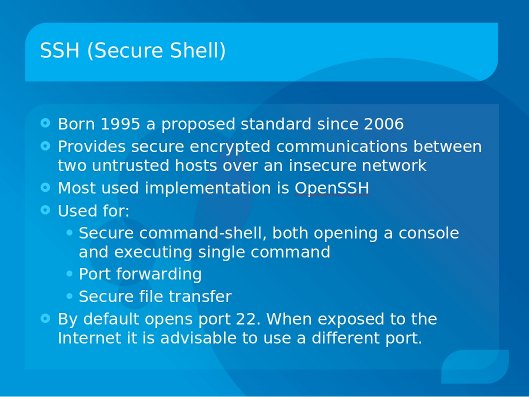
Different implementations of SSH will have slightly different features. In this case I will focus on OpenSSH.
To install on the server (Debian/Ubuntu):
sudo aptitude install openssh-server
To install on the server (Redhat/Fedora):
sudo yum install openssh-server
To start/stop/restart under Debian/Ubuntu
sudo /etc/init.d/ssh start
sudo /etc/init.d/ssh stop
sudo /etc/init.d/ssh restart
To start/stop under RedHat/Fedora
service sshd start
service sshd stop
service sshd restart
confirming that the port is open
To check that the port is open by name
netstat -l | grep -i ssh
Or faster and more specific, to check by port number
netstat -ln | grep 22
Note: if you configure SSH to listen to a different port as explained later in this post, replace 22 with the port configured.
Once the server is running you can connect from other computers as long as the port is not blocked by a firewall.
Command examples
SSH has many parameters. They are described on the man pages
man ssh
Here are some basic (and very common) examples:
The basic command to connect to a server (host) assumes that ssh is listening to port 22 and that you want to connect with the same userID as you are using on the local computer. Host name is the only mandatory parameter:
ssh 192.168.1.100
or
ssh mycomputer.com
Connecting using a userID "rarsa" on the remote computer
ssh rarsa@mycomputer.com
or
ssh mycomputer.com -l rarsa
When the server is listening to a different port
ssh -p 50022 rarsa@mycomputer.com
Using SSH to copy files
Sometimes you will need to copy a file (or folder) from your local computer to a computer where you have SSH access. SSH provides a command that allows you to do a secure copy "scp"
The main parameters are:
- The file name for the file you want to transfer
- The address of the remote computer, and user id if you are using a different one
- The destination path and name
scp "source" "destination"
Source and destination can be fully qualified indicating the userID, server name, destination path
scp file rarsa@192.168.1.102:/destinationPath/file
You can copy directories recursively and between other hosts and use different ports
scp -P 50022 -r rarsa@192.168.1.101:/sourcePath/directory rarsa@192.168.1.102:/destinationPath/directory
X forwarding
OK, accessing the remote computer and executing commands is handy and exciting and maybe all you need to do, but what if you want to run a graphical application on the remote computer?
ssh has the -X parameter that allows the GUI of the remote program to display on your local computer
First ssh to the remote computer
ssh rarsa@mycomputer.com -X
Then on that console, execute the program. e.g. to run Firefox:
firefox
The program will be actually running on the remote computer but the Graphical interface will show in the local computer!
Note: When using X forwarding this way, we refer to the program running on the remote computer as "the client" and to the local computer displaying the GUI as "the server".
Port forwarding/tunneling
One of the most powerful features of SSH is the ability to "forward ports" sometimes referred as "tunneling"
Port forwarding allows forwarding of TCP/IP connections to a remote machine over an encrypted channel.
This is, imagine that you need to FTP (port 21) to a remote computer which is behind a firewall that only allows SSH connections.
ssh rarsa@remotecomputer.com -L50021:localhost:21
This command will "tunnel" the FTP traffic from port 50021 on the local computer to port 21 on the remote computer
Now you can ftp to the remote computer with the following command
ftp localhost 50021
Note, you can specify any available port you want on the local computer, but you must specify the correct port listening on the remote computer
Reverse tunneling
If you want the remote computer to access a port on yours but you are behind a firewall that closes all incoming ports, you do "reverse tunneling"
You first connect to the remote computer specifying that the a port on the remote computer will be forwarded to a port in your computer. For example, for FTP:
ssh rarsa@remotecomputer.com -R50021:localhost:21
Now the remote computer can FTP to your computer using port 50021.
Note: you can specify any available port you want on the remote computer, but you must specify the correct port listening on the local computer).
Combining it all
You can tunnel (and reverse tunnel) various ports on the same ssh command.
You can even indicate that the remote computer should forward to a different server!
For example, to allow your computer to FTP to the remote computer and at the same time allow the remote computer to SSH to your computer and at the same time forwarding port 80 to the web server in the same network
ssh rarsa@remotecomputer.com -L50021:localhost:21 -R50022:localhost:22 -L8080:webserver.com:80
I personally use reverse tunneling to SSH to my father's computer which is behind a firewall. He just needs to execute the ssh command to connect to my computer opening a reverse tunnel for port 22, I can then SSH back to his computer using the reverse tunnel.
On my father's side (assuming he has a "dad" id on my computer):
ssh dad@mycomputer.com -R50022:localhost:22
On my computer (assuming I have a "rarsa" id on his computer:
ssh rarsa@localhost
Configuration
The ssh client takes it's parameters, in order of precedence from:
1. Command line parameters
2. User configuration file ~/.ssh/config
3. System-wide configuration file /etc/ssh/ssh_config
The sshd server daemon takes it's parameters, in order of precedence from:
1. Command line parameters
2. System-wide configuration file /etc/ssh/sshd_config
Server configuration file
/etc/ssh/sshd_config
Note: you must restart the SSH daemon after modifying the configuration file
For example, to prevent portscans use a different port by editing sshd_config and specifying the port.
port 50022
You can look at all the options on the man pages
man sshd_config
Client configuration file
As we've seen before, the SSH command can get quite long. If you normally use the same parameters in general or particular parameters for a remote server, you can configure all that on your local SSH configuration file
~/.ssh/config
For more detailed information:
The man pages:
man ssh
man sshd
man ssh_config
man sshd_config
The OpenSSH website:
http://www.openssh.org/
The web:
There are some very good examples of port forwarding, just search for them.
For example
http://souptonuts.sourceforge.net/sshtips.htm
Comments
There are Windows
There are Windows equivalents - useful as clients for these servers, or as servers for these clients.
Typically, there are two ways to go about this - standalone, or as part of Cygwin.
(http://www.openssh.org/windows.html)
For standalone: http://sshwindows.sourceforge.net/
(At least I think that's where I got mine from.)
As part of a larger cygwin installation (LOTS of goodies here, well beyond just ssh): http://cygwin.com/
- after installation, particularly of the ssh server package, everything is almost exactly the same as described in the blog post. Probably the hardest part is getting used to the file structure / configuration file locations.
- http://cygwin.com/packages/
- substantially, these are Linux equivalent command line facilities. Graphics, X, KDE, etc., are out there, but not as solid as base / command line cygwin itself.
There are lots of Windows VNC servers/clients out there:
- my favourite: TightVNC - http://www.tightvnc.com/
- very popular: http://www.realvnc.com/
- also very popular: http://www.uvnc.com/